White Note Fantasy, Part II
Stephen Soderberg
REFERENCE: MTO Vol. 4, No. 3
KEYWORDS: John Clough, Jack Douthett, David Lewin, maximally even set, microtonal music, hyperdiatonic system, Riemann system
ABSTRACT: This article is a continuation of White Note Fantasy, Part I, published in MTO Vol. 4, No. 3 (May 1998). Part II combines some of the work done by others on three fundamental aspects of diatonic systems: underlying scale structure, harmonic structure, and basic voice leading. This synthesis allows the recognition of select hyperdiatonic systems which, while lacking some of the simple and direct character of the usual (“historical”) diatonic system, possess a richness and complexity which have yet to be fully exploited.
Copyright © 1999 Society for Music Theory
II. A Few Hypertonal Variations
6. The usual diatonic as a model for an abstract diatonic system
7. An abstract diatonic system
8. Riemann non-diatonic systems
9. Extension of David Lewin’s Riemann systems
[5.1] Consider a symmetric interval string of cardinality n = c+d which contains c interval i’s and d interval j’s. If the i’s and j’s in such a string are additionally spaced as evenly apart from one another as possible, we will call this string a “necklace.” If s is a string in Cn and p is an element of Cn, then the structure ps is a “necklace set.” Thus <iijiij>, <ijijij>, and <ijjijjjijjj> are necklaces, but <iijjii>, <jiijiij>, and <iijj>, while symmetric, are not necklaces. i and j may also be equal, so strings of the form <iii...> are valid necklaces. Specific necklaces can be formed by substituting any appropriate integers for i and j; e.g., <113113>, <772772>, <8181818>, and <23323332333>. If s = <181> and p = 3, then ps = {3,4,2} is a necklace set in C10.
[5.2] MAXIMALLY EVEN STRINGS. After John Clough and Jack Douthett,(1) we will define a
maximally even (ME) interval string <m;n> as the string of m intervals in Cn (so m
<= n) that meets two criteria:
(1) <m;n> is a necklace;
(2) the elements of <m;n> are either k or
k+1.
If s = <m;n> is a maximally even string, and p is an element of Cn, then the
structure ps will be called a maximally even set. Familiar examples of ME strings are
<23223> (pentatonic), <2212221> (diatonic), <222222> (whole-tone), and
<21212121> (octatonic). While we will be concentrating mostly on generalizing the
diatonic, it will become apparent that many of our results will apply to other ME, and
even non-ME, necklaces.
[5.3] ME STRING TOKENS. As pointed out by Clough and Douthett, m and n determine a unique ME set, i.e., <m;n> = <p;q> iff m=p and n=q. Thus our notation is both necessary and sufficient to identify an ME string. But, although all ME strings are necklaces while all necklaces are not ME, any ME string can be taken as a token for an infinite “class” of necklaces. For instance, s = <1121112> is maximally even, but all strings of the form <xxyxxxy> are necklaces, whether they are ME or not (e.g., <2212221> is ME, <1161116> is not ME, <5525552> is not ME, <5565556> is ME, etc.) Thus we will use the notation <(m;n)> to denote the class of all necklaces that can be derived from <m;n> by substituting other integers for <m;n>’s elements. <(7;12)> then denotes all strings of the form <xxyxxxy>, and we will write <(7;12)> DEF <9222922> if we need a specific string example from the class.(2) The need for specification is due in part to the fact that WARP is sensitive to the rotation of its generic and scale strings, as will now be made evident.
[5.4] MAXIMALLY EVEN WARPS. If q = <u;v> and r = <v;w> are ME strings, they automatically fulfill the inequality conditions in the definition for the r-WARP of q: (u = #(q)) <= (v = SUM(q) = #(r)) <= (w = SUM(r)). <u;v> serves as a generic string and <v;w> as a scale string. But generally, two necklaces q = <(u;v)> and r = <(v;w)> are not WARP-compatible unless SUM(q) = #(r).
[5.5] Let q = <3;11> and r = <11;13> be two ME strings. If we stipulate permutations q = <3;11> DEF <344> and r = <11;13> DEF <11211111211>, then WARP(q,r) = <445>, and the resultant string is a permutation of the ME string <3;13>. But if we choose a different permutation of q, q’ = <3;11> DEF <434>, WARP(q’,r) = <535> which, although it is a necklace in the <(3;13)> class, is not ME. Now let x = <11;18> DEF <12212212212>. WARP(q,x) = <567> and WARP(q’,x) = <657>, both of which are asymmetric (and thus, of course, neither ME nor necklaces). If we generalize without caution, the WARP may be undefined. For example, if p = <(3;11)> DEF <177>, then WARP(p,r) is undefined since SUM(p) = 15 does not equal #(r) = 11; but if p’ = <(3;11)> DEF <155> we have WARP(p’,r) = <166>.
[5.6] Again let q = <3;11> DEF <344>. If we now stipulate the 0- permutation of the scale string as r(0) = <11;13> DEF <11211111211>, then WARPSET(q,r) = {<445>, <445>, <454>, <355>, <355>, <355>, <445>, <454>, <454>, <355>, <355>}. Let a = <445>, a’ = <454>, and b = <355>; then CHORDSET(q,r) (based on the scale {0,1,2,4,5,6,7,8,9,11,12}) is {0a, 1a, 2a’, 4b, 5b, 6b, 7a, 8a’, 9a’, 11b, 12b}.(3)
[5.7] While much of what we are about to discuss can be said about necklaces generally, it will be most profitable to concentrate on maximal evenness, but we will still generalize when doing so points to interesting relations and structures. We will now adopt the following notation for WARPSETs whose generic and scale strings are both maximally even:
WARPSET(<u;v>,<v;w>) = ||u;v;w||
Thus the designation “maximally even” applied to a WARP refers only to the variable strings (i.e., the generic and scale strings) since, as noted, resultant strings may not be maximally even.
[5.8] I = <x;x> is a left identity (generic) string, and J = <y;y> is a right identity (scale) string for ME WARPs. Thus WARP(I,<x;y>) = WARP(<x;y>,J) = <x;y>.
[5.9] DIATONIC STRINGS. Using Clough and Douthett’s Theorem 2.2,(4) for any odd x > 1, a diatonic string is any ME string of the form d = <x;2(x-1)> = <j,1,k,1>, where j is a substring of (x-3)/2 2’s and k is a substring of (x-1)/2 2’s. For any pitch class p, pd is a (hyper)diatonic set based on p. For p=0,
x 2(x-1) d (p,d)
3 4 <121> {0,1,3}
5 8 <21221> {0,2,3,5,7}
7 12 <2212221> {0,2,4,5,7,9,11}
9 16 <222122221> {0,2,4,6,7,9,11,13,15}
... ... ... ...
We will now focus closely on WARPSETs of the form ||w;x;2(x-1)|| and their related CHORDSETs as we generalize the usual diatonic.
6. The Usual Diatonic as a Model for an Abstract Diatonic System
[6.1] RD(1). To model the usual diatonic in the notation presented in Part I, we will make the following assignments:
In C7,
J = <7;7> = <1111111>
g = <3;7> DEF <223>
p = 0
X = WARPSET(g,J) = ||3;7;7||
Y = pJ = {0,1,2,3,4,5,6}
Z = CHORDSET(X)
and in C12,
h = <7;12> DEF <2212221>
q = 0 W = WARPSET(g,h) = ||3;7;12||
H = qh = {0,2,4,5,7,9,11}
K = CHORDSET(W)
The usual diatonic system,(5)in our present terminology (see [2.25]), is then the ordered triple
RD(1) = (W,H,K).
Since (X,Y,Z) (=) (W,H,K), the entire model can be displayed as a set of correspondences:
___________C7_____________ ___________C12______________
/ \ / \
X Y Z W H K
<223> = g 0 {0,2,4} = 0g <435> = t 0 {0,4,7} = 0t
<223> = g 1 {1,3,5} = 1g <345> = t’ 2 {2,5,9} = 2t’
<223> = g 2 {2,4,6} = 2g <345> = t’ 4 {4,7,11} = 4t’
<223> = g 3 {3,5,0} = 3g <435> = t 5 {5,9,0} = 5t
<223> = g 4 {4,6,1} = 4g <435> = t 7 {7,11,2} = 7t
<223> = g 5 {5,0,2} = 5g <345> = t’ 9 {9,0,4} = 9t’
<223> = g 6 {6,1,3} = 6g <336> = u 11 {11,2,5} = 11u
Names for the strings <435> = t, <345> = t’, and <336> = u have been assigned to identify the usual major, minor, and diminished triads respectively.(6)
[6.2] The interval matrix for the diatonic scale string, which is not partitioned, is
/ 2 5 0 0 0 0 0 0 0 0 0 0 \
| 0 0 4 3 0 0 0 0 0 0 0 0 |
| 0 0 0 0 6 1 0 0 0 0 0 0 |
MINT(h) = | 0 0 0 0 0 1 6 0 0 0 0 0 |
| 0 0 0 0 0 0 0 3 4 0 0 0 |
| 0 0 0 0 0 0 0 0 0 5 2 0 |
\ 0 0 0 0 0 0 0 0 0 0 0 7 /
and this yields the ic-mapping
in C7 in C12
1 --> 1,2
2 --> 3,4
3 --> 5,6
4 --> 6,7
5 --> 8,9
6 --> 10,11
7 --> 12 (=0)
As noted above, dealing with non-partitioned interval matrices can be somewhat complex, and we purposely have chosen examples which avoid them. However, in this case, the ambiguity presented by the tritone does not present any unusual difficulties. If we wish to write the vector associated with MINT(h), it is helpful to display it thus:
U(h) = [254361
1634527]
instead of [254362634527]. The vector can then be “partitioned” as
[2,5;4,3;6,1
1,6;3,4;5,2;7]
so that
U’(h) = [2+5;4+3;6+1;
1+6;3+4;5+2;7] = [7777777] = U(J)
Keeping the usual caution in mind while dealing with the tritone in vector applications, we can then write the corresponding interval-class vector relationships on which generic covariance is based:
V(h) = [254361]
V’(h)= [2+5;4+3;6+1] = [777] = V(J)
[6.3] Thus by G-COV, the partition sum ic-vector of any string in W will equal V(g). W contains only two unique strings, t (t’) and u, for which V(t) = V(t’) = [001110] and V(u) = [002001], so V’(t) = V’(t’) = [0+0;1+1;1+0] = V’(u) = [0+0;2+0;0+1] = [021] = V(g). If we had chosen a different string for g we would have created a different white note system, but by G-COV the same partition-vector pattern would still hold due to the diatonic scale string being held constant; however, we would then be headed in a direction which would soon diverge radically from our chosen diatonic model.
[6.4] The important thing to take from G-COV, with respect to RD systems, is the characteristic partition pattern imposed by the scale string which will always be of the int-multiplicity form
[a,b; c,d; ...; p,q;
q,p; ...; d,c; b,a; z]
and which can always be reduced to the ic-multiplicity form
[a,b; c,d; ...; p,q].
The sum of the elements in any comma-separated pair in both forms will always equal the sum of the elements in the scale string (i.e., z).
[6.5] To investigate scale covariance in RD(1) we now concentrate on ic-vectors spanning sets in the generic system (X,Y,Z). From this point on, when dealing with ic-vectors, we will adopt the more intuitive and widely used notation which places the ic0 multiplicity as the first vector component. Thus V(pg,(p+1)g) = [0513] for g = <223> indicates that between the sets, say, {1,3,5} and {2,4,6}, there are 0 ic0’s (no common tones), 5 ic1’s, 1 ic2, and 3 ic3’s.
[6.6] Given the generic string g = <3;7> DEF <223> as before, if p is any
pitch class in C7, then pg is a triad in Z and (p+t)g is pg’s t-transpose. The following
list exhausts the possible ic spanning vectors for Z (% indicates plus-or-minus)
V(pg,pg)
= [3042]
V(pg,(p%1)g) = [0513]
V(pg,(p%2)g) = [2142]
V(pg,(p%3)g) = [1323]
The distribution of components in this list isn’t as random as it might at first appear
since it derives from the list of interval spanning vectors U. The reader will note that
the ic-vector is simply the int-vector with the non-zero components “folded
back” on their inversions. For U(pg,(p+1)g) we have:
[ 0 3 0 2 1 1 2 ]
| | | | | | |
int: 7=0 1 2 3 4 5 6
ic: 0 1 2 3 3 2 1
\ \ \___/ / /
\ \_________/ /
\_______________/
and [0302112] --> [0513]. The pattern behind the ic vectors listed is then made clear by listing the int vectors for the same sets:
U(pg,(p+1)g) =
[3021120]
U(pg,(p+2)g) =
[0302112]
U(pg,(p+3)g) =
[2030211]
U(pg,(p+4)g) =
[1203021]
U(pg,(p+5)g) =
[1120302]
U(pg,(p+6)g) =
[2112030]
U(pg,(p+0)g) =
[0211203] (= U(g))
(note that we retain the ic0 component in the last position here since this display is taken directly from MINT(g)—see [3.11–14] in Part I).
[6.7] We can now relate any ic vector spanning two sets in K to one of the spanning vectors just listed for Z since, by S-COV, the partition- sum ic vector spanning any pair of sets in K will equal the ic vector spanning a corresponding pair of sets in Z. Some examples, referring back to the system correspondences in [6.1], are:
V(9t’,2t’) = [1121130]
V’(9t’,2t’) = [1;1+2;1+1;3+0]
= [1323]
= V(5g,1g)
V(4t’,5t) = [0230121]
V’(4t’,5t) = [0;2+3;0+1;2+1]
= [0513]
= V(2g,3g)
V(5t,7t) = [0141021]
V’(5t,7t) = [0;1+4;1+0;2+1]
= [0513]
= V(3g,4g)
[6.8] By S-COV, the list of ic spanning vectors in [6.6] summarizes all the voice-leading possibilities for any pair of triads in Z and thus in K as well. If we display this list as an “available voice-leading” matrix for interval classes,
/3042\
AVLIC(Z) = |0513|
|2142|
\1323/
it can be read in two ways. First, any given row indicates the multiplicity of generic interval classes spanning two triads in Z or the multiplicity of diatonic interval classes spanning two corresponding triads in K. For example, row 3 indicates the voice- leading multiplicities found in V(pg,(p%2)g), so all seven of the corresponding chord pairs in K (whose “roots are a major or minor third apart”) have available connections of 2 ic0, 1 ic1/ic2, 4 ic3/ic4, and 2 ic5/ic6. Second, any column will list all possible chord pairs spanned by a given interval class. If we wish to conduct an “interval class search”—say we wish to know how all possible chord progressions in K are spanned by a perfect or diminished fifth - - we simply go to the fourth column (representing ic3 in C7 which corresponds to ic5/ic6 in C12) and read down: there are 2 fifths available between correspondents of pg and pg; 3 fifths between correspondents of pg and (p%1)g; 2 between corespondents of pg and (p%2)g; and 3 between correspondents of pg and (p%3)g.
[6.9] We can also form the more complete “available voice-leading” matrix for intervals,
/3021120\
|0302112|
|2030211|
AVLINT(Z) = |1203021|
|1120302|
|2112030|
\0211203/
and make interval-spanning statements about corresponding chords of the same sort as we did for interval-class spans. Due to AVLINT’s symmetry ((row m, column n) = (row n, column m)), we can state a more general theorem relating chord pairs which can be extended via S-COV to correspondence-related white note systems. We state it here without proof and using int rather than ic notation.
[6.10] For any integers p,x,y in the chromatic white note system (A,B,C) which has been generated by a generic string g,
#intx(pg,(p+y)g) = #inty(pg,(p+x)g).
For example, returning to g = <2,2,3> and (X,Y,Z) in the usual diatonic world, this theorem tells us, among many other things, that #int5(pg,(p+1)g) = #int1(pg,(p+5)g) = 1. To give us some idea of the amount of information packed into an AVLIC or AVLINT matrix, we can translate this example (by correspondence) into more familiar diatonic language, remembering that int5 and int1 in C7 “translate” to int(8- or-9) and int(1-or-2), respectively, in C12. What the example says, loosely, is that there is always one (and only one) 6th within a diatonic scale that can be found to span two triads within that scale whose roots are a 2nd apart and furthermore this implies that there is always one (and only one) 2nd within that same scale that can be found to span two triads within that scale whose roots are a 6th apart.
[6.11] The theorem in [6.10] will, of course, hold for any simple white note system, not only those generated by ME strings. Its application is intimately related to the principle of scale covariance, since changing the scale string while keeping the generic string will consistently yield the same values for corresponding sets, but changing the generic string will normally yield different AVLINTs.(7)
[6.12] Finally, cover covariance (C-COV) in RD(1) is particularly interesting. The C-7 chromatic scale Y = {0,1,2,3,4,5,6} can be covered by the g-triads in Z in a number of ways, but we know that any minimal cover of Y must consist of three triads. Perhaps the most important cover of Y is the one which, by correspondence, underlies the “dominant” related triples in K:
COVER1(Z) = {pg, (p+3)g, (p-3)g}.
For istance, setting p = 5, R = {5g,1g,2g} = {{5,0,2},{1,3,5},{2,4,6}} and R//Y (see [4.16-19] in Part I). Also note the common-tone relationships among these triads: #int0(pg,(p+3)g) = #int0(pg,(p-3)g) = 1 but #int0((p+3)g,(p-3)g) = 0. The only other minimal cover from Z is of the form
COVER2(Z) = {pg, (p+1)g, (p-1)g}.
with the common-tone relationships: #int0(pg,(p+1)g) = #int0(pg,(p- 1)g) = 0 and #int0((p+1)g,(p-1)g) = 2. Any triple in Z which cannot be expressed in one of these two forms (COVER1 or COVER2) will not cover Y (e.g., {0g,2g,3g} will not cover Y).
[6.13] Now, bracketing possible psycho-acoustical, semiological, sociological, and historical “reasons” (which we’ve at least been trying to avoid up until now at any rate—saving them for later to sit in judgement on any synthetic structures we might come to enjoy), is there any reason that we might expect a privileged status for either COVER1 or COVER2? This is tantamount to asking: Is there really any (non-bracketed) reason to “prefer” progressions whose roots are a diatonic 4th-or-5th apart to those whose roots are a 2nd-or-7th apart, or vice versa? Well, if we examine the possible (diatonicized) triads in K corresponding to the sets in Z (refer back to the correspondence chart in [6.1]), we note that, for whatever choice we make for a correspondence to COVER2, the resulting cover of H will be “mixed” with respect to chord “quality.” For example, the cover {2t’,4t’,5t} contains two minor and one major triad. On the other hand, the choices corresponding to COVER1 yield two possibilities: “mixed” and “pure.” With respect to symmetry, COVER1 can retain the kinds of (mirror) “quality” symmetries found in COVER2 while adding a kind not found there: two unique covers which each contain three chords of the same quality. Furthermore, COVER1 seems to most directly point to the overall inversional symmetry at the heart of RD(1) through the partition of K by major, minor, and diminished chords:
R1(Z) = {5t,0t,7t}
R1’(Z) = {2t’,9t’,4t’}
R2(Z) = {11u} where R2
is a sort of “residue” set.
So, fully aware that this is a choice made, in this particular context, by a preference for maximal symmetry coupled with a desire to discover as much variety as possible, we will privilege the sets R1 and R1’ and call them “Riemann covers.”(8)
[6.14] A Riemann cover R will always have the following characteristics ($(A) indicates the interval string associated with set A):
- The set R contains three chords which will be labelled S, T, D.
- #int0(S,T) = #int0(T,D) = 1
- #int0(S,D) = 0
- $(S) = $(T) = $(D)
- V(T,S) = V(T,D)
- S.&.T.&.D = H
- There is an inversion of R, R’ = {S’,T’,D’}, such that R’ is a Riemann cover.
[6.15] Any CHORDSET whose scale string is (hyper)diatonic and that generates a Riemann cover will be called a Riemann Diatonic (RD) system. As we shall soon see, the usual diatonic based on ||3;7;12||, which we have been calling RD(1), represents the “smallest” or “first” such system available. This represents a somewhat different approach to what David Lewin has called “Riemann Systems”.(9) The two approaches will be reconciled shortly, but a more complete congruence will not be demonstrated at this time. Our purpose here is more toextend systems rather than to simply find an alternate path to those that are known (and have been extensively used) in C12.
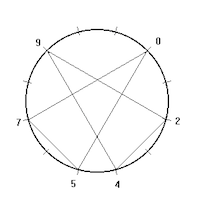
[6.16] The triple {S,T,D} and its inversion display a characteristic pattern when projected onto a C12 circle. We plot the “roots” of each chord triple {5t,0t,7t} and {2t’,9t’,4t’} as vertices for the two triangles (5,0,7) and (2,9,4) on C12 (see Figure 1). Note that the two triangles overlap one another. A more complex version of this configuration will be met in RD(2)’s Riemann covers where we will find four overlapping triangles. In other words, where RD(1) has two “natural tonics” (the apexes of the triangles—one (right) “major” and one (left) “minor”), RD(2) will have four “natural” tonics, each supported by its own “dominant” and “subdominant.” In general, any system RD(n) (to be defined) will have 2n, or n pairs of, Riemann covers.
[6.17] Note that nothing has yet been said about the cardinality of the basic RD(1) chords, so in higher RD systems the basic chords need not be triads. Nor has any stipulation been made concerning the specific shape (string) of the chords, so “dominant,” “mediant,” and any other intervallic constituents are temporarily left undefined.
7. An Abstract Diatonic System
[7.1] Let us assume that the set of strings W = ||3;7;12|| in RD(1) is the first member of a series of similar RD WARPSETs ||x;y;z||. We first note, given that the scale string <y;z> must be diatonic (an assumption that can be stretched within limits—see [] below), there can’t be any other WARPSET of the form ||3;y;z|| since (from [6.14]) chord T must have one (and only one) tone in common with both S and D, and only y=7 satisfies that condition, concomitantly fixing z=12. So we begin by varying x. x=4 won’t work since, to satisfy the common- tone condition, this would imply a WARPSET of the form ||4;10;z||, and <10;z> can’t be diatonic since 10 is even; and the same applies for any even x. x=5 is the next possibility. Here the common-tone condition demands a WARPSET of the form ||5;13;z||, and the diatonic string from y=13 is <13;24>. In fact, as we will now see, the system (W’,H’,K’) based on ||5;13;24||, which will be labelled RD(2), is the next RD system. After confirmation of this fact, we will return to find a general expression for any RD system.
[7.2] RD(2). We begin by making the following assignments:
In C13,
J’ = <13;13> = <1111111111111>
g’ = <5;13> DEF <23233>
p = 0
X’ = WARPSET(g’,J’) = ||5;13;13||
Y’ = pJ’ = {0,1,2,3,4,5,6,7,8,9,10,11,12}
Z’ = CHORDSET(X’)
and in C24,
h’ = <13;24> DEF <2222212222221>
q = 0
W’ = WARPSET(g’,h’) = ||5;13;24||
H’ = qh’ = {0,2,4,6,8,10,11,13,15,17,19,21,23}
K’ = CHORDSET(W’)
[7.3] Since (X’,Y’,Z’) (=) (W’,H’,K’), we can display RD(2) fully by the following table of correspondences:
____________C13_______________ _______________C24_________________
/ \ / \
X’ Y’ Z’ W’ H’ K’
<23233>=g’ 0 {0,2,5,7,10} = 0g’ <46365> = r 0 {0,4,10,13,19} = 0r
<23233>=g’ 1 {1,3,6,8,11} = 1g’ <45465> = s’ 2 {2,6,11,15,21} = 2s’
<23233>=g’ 2 {2,4,7,9,12} = 2g’ <45465> = s’ 4 {4,8,13,17,23} = 4s’
<23233>=g’ 3 {3,5,8,10,0} = 3g’ <45456> = s 6 {6,10,15,19,0} = 6s
<23233>=g’ 4 {4,6,9,11,1} = 4g’ <36456> = r’ 8 {8,11,17,21,2} = 8r’
<23233>=g’ 5 {5,7,10,12,2}= 5g’ <36456> = r’ 10 {10,13,19,23,4}= 10r’
<23233>=g’ 6 {6,8,11,0,3} = 6g’ <46365> = r 11 {11,15,21,0,6} = 11r
<23233>=g’ 7 {7,9,12,1,4} = 7g’ <46365> = r 13 {13,17,23,2,8} = 13r
<23233>=g’ 8 {8,10,0,2,5} = 8g’ <45465> = s’ 15 {15,19,0,4,10} = 15s’
<23233>=g’ 9 {9,11,1,3,6} = 9g’ <45456> = s 17 {17,21,2,6,11} = 17s
<23233>=g’ 10 {10,12,2,4,7}=10g’ <45456> = s 19 {19,23,4,8,13} = 19s
<23233>=g’ 11 {11,0,3,5,8} =11g’ <36456> = r’ 21 {21,0,6,10,15} = 21r’
<23233>=g’ 12 {12,1,4,6,9} =12g’ <36366> = t 23 {23,2,8,11,17} = 23t
[7.4] We will not give the 13X24 interval matrix MINT(h’) here, but we will note the ic-mapping it generates for RD(2):
j-in-C13 k-in-C24
1 --> 1,2
2 --> 3,4
3 --> 5,6
4 --> 7,8
5 --> 9,10
6 --> 11,12
7 --> 12,13
8 --> 14,15
9 --> 16,17
10 --> 18,19
11 --> 20,21
12 --> 22,23
13(=0)--> 24(=0)
[7.5] Illustrating the situation for G-COV in RD(2), the partition vectors produce the following (where a=10, b=11, c=12, d=13):
U(h’) = [2b496785a3c1
1c3a587694b2d]
U’(h’) = [2+b;4+9;6+7;8+5;a+3;c+1;
1+c;3+a;5+8;7+6;9+4;b+2;d]
= [ddddddddddddd] = U(J’)
V(h’) = [2b496785a3c1]
V’(h’) = [2+b;4+9;6+7;8+5;a+3;c+1] = [dddddd] = V’(J’)
W’ contains three unique strings, r (r’), s (s’), and t, for which
V(r) = V(r’) = [001112003110],
V(s) = V(s’) = [000221003110],
V(t) = [002003004001].
Thus
V’(r) = V’(r’) = [0+0;1+1;1+2;0+0;3+1;1+0] =
V’(s) = V’(s’) = [0+0;0+2;2+1;0+0;3+1;1+0] =
V’(t) = [0+0;2+0;0+3;0+0;4+0;0+1] =
= [023041] = V(g’).
[7.6] For ic “voice leading” in RD(2) we have
/5046082\
|0732715|
|2354344|
AVLIC(Z’) = |3246163|
|0731905|
|4146082|
\1543525/
By S-COV we can then determine that, for example, when we move from the chord 8r’ to the chord 17s, with a span of 5 generic ic steps between “roots,” that V(8r’,17s) corresponds to V(pg’,(p%5)g’) = [4146082], which means that between 8r’ and 17s there are available 4 ic0 connections, 1 ic1/2, 4 ic3/4, ..., 2 ic11/12. Leaving out the trivial case of the progression pg’-->pg’, there are a total of 6X13=78 possible triad progressions in RD(2). This is in contrast to 3X7=21 possible triad progressions in RD(1). In RD(1) there are 10 distinct spanning vectors; in RD(2) there are 30. All of this is summarized in detail in Table 1 for RD(1) and Table 2 for RD(2).
|
Table 1 (click to enlarge and see the rest) |
Table 2 (click to enlarge and see the rest) |
[7.7] That RD(2) is indeed a Riemann diatonic system can now be demonstrated by investigating its C-COV relationships. The C13 chromatic scale Y’ can be minimally covered by three pentachords from Z’ in two ways. Following RD(1), and our preference for maximal symmetry, we will select
COVER(Z’) = {pg’, (p+6)g’, (p-6)g’}.
This in turn discloses the following partition of the chords in K’:
R1(Z’) =
{0r,11r,13r}
R1’(Z’) =
{21r’,8r’,10r’}
R2(Z’) = {6s,17s,19s}
R2’(Z’) =
{15s’,2s’,4s’}
R3(Z’) = {23t}.
It is easily verified from [6.14] that R1, R1’, R2, and R2’ are Riemann covers.
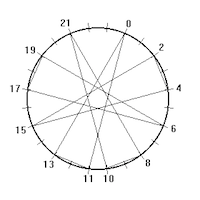
[7.8] We may now see the characteristic triangular pattern for RD(2) alluded to in [6.16]. If we plot the roots of each of the four Riemann covers as sets of vertices on the C24 circle, (0,11,13), (21,8,6), (6,17,19), and (15,2,4), we note again that these four (congruent) triangles all cross one another in a characteristic “RD pattern” first suggested in [6.16] (see Figure 2).
[7.9] We now return to finding a general expression for any Riemann Diatonic system RD(n). First note that both generic strings <223> = <3;7> for RD(1) and <23233> = <5;13> for RD(2), which are not themselves diatonic, can be derived from the diatonic strings <112> = <3;4> and <12122> = <5;8>, respectively, by simply adding 1 to each entry in the strings. Thus <223> = <1+1,1+1,2+1> = <3;4+3> = <3;7> and <23233> = <1+1,2+1,1+1,2+1,2+1> = <5;8+5> = <5;13>. Generally, any ME string <x;y+kx> can be derived by writing out the ME string <x;y> and then adding k to each entry in the string. But apparently only k=1 will produce a generic string which can be used as a basis for the type of RD string we have been looking at.
[7.10] In any RD WARPSET ||x;y;z|| there is a “hidden” diatonic string <x;y’> such that the generic <x;y> = <x;y’+x>, and since (by [5.9]) y’= 2(x-1), any RD WARPSET can be expressed in the form ||x;3x-2;6(x-1)|| for odd x > 1.
[7.11] <x;3x-2> = <2,j,2,k> (where j is a substring of (x-3)/2 3’s and k is a substring of (x-1)/2 3’s) will be called a Riemann generic string. Thus RD(3)’s generic string is <2332333> (whose “hidden” diatonic string is, incidentally, also the usual diatonic scale string <1221222>).
[7.12] RD(n). We may also express any higher RD system in terms of RD(1) as its generator. Thus any RD WARPSET can also be expressed as ||3+2n;7+6n;12+12n|| where n >= 0. By simple algebraic manipulation, we may then define a generalized RD system as RD(n) = (A,B,C), where A = ||2n+1;6n+1;12n|| for n>0.
8. Riemann Non-Diatonic Systems
[8.1] Riemann covers, which we have seen are a significant characteristic of RD systems, may also be associated with non-diatonic systems. The following general string set formulae assume that x is odd and greater than 1, y=3x-2, and k >= 0. Other variations beyond those given here are possible and finding them is a fruitful exercise.
[8.2] The simplest case is ||x;y;(k+1)y|| which represents a series of “smoothly” expanding string sets. CHORDSET(<x;y>,J), where J=<y,y> is a string of y 1’s, will trivially generate y Riemann covers of the form {pq,(p+z)q,(p-z)q}, where p is a pitch class in Cy, q is some stipulated string in <x;y>, and z = [y/2]. We already know that this triple will be a cover, but it is also a Riemann cover since all three chords share the string q. <y;(k+1)y> then simply enlarges all intervals in the scale string <y;y> by the same amount which concomitantly enlarges all intervals in q by the same amount, keeping the Riemann cover relationship for any k.
[8.3] ||x;y;6(x-1)+ky|| represents an expansion of RD(n)’s scale string by adding multiples of y. ||x;y;6(x-1)|| is the basic formula for RD(n) given above in [7-10]. Adding k to each entry in a diatonic string expands the string into another ME necklace form, keeping the original ME pattern. Thus <7;12> = <2212221> and <7;12+7> = <7;19> = <3323332> retains the basic ME pattern. When this happens, the initial composite WARPSET’s resultant strings are uniformly increased by successively adding the (constant) generic string to each of those resultant strings. To continue the example, stipulating <3;7> = <223>, we have ||3;7;12|| = {<435>,<345>,...,<336>}, so (by adding <223> to each of these strings) ||3;7;12+7|| = ||3;7;19|| = {<4+2,3+2,5+3>,<3+2,4+2,5+3>,...,<3+2,3+2,6+3>} = {<658>,<568>,...,<559>}. Since the relative positions of identical strings are retained, the Riemann cover is likewise retained.
[8.4] Perhaps the most interesting Riemann non-diatonic system is based on what might be termed the “conjugate-diatonic” WARPSET, ||x;y;3x||. While the generic string <x;y> is again retained, the values of the elements of the diatonic scale string are reversed; so the diatonic <2212221> becomes the “conjugate-diatonic” <1121112>.
[8.5] Two ME strings s = <x;ax+b> and t = <x;ax+b’> are conjugates of one another if b+b’ = x. Thus <5;4X5+3> = <5;23> = <45455> and <5;4X5+2> = <5;22> = <54544> are conjugates. To find the conjugate of the general scale string in RD(n) we first note that, through simple manipulation, <3x-2;6(x-1)> = <3x-2;(3x-2)+(3x-4)>. Since (3x-2)-(3x-4) = 2, the conjugate-diatonic scale string will be of the form <3x-2;(3x-2)+2> = <3x-2;3x>.
[8.6] Swapping the diatonic scale string for its conjugate has the effect of changing the string’s values while retaining its basic ME pattern, thereby retaining the Riemann cover as well. For example, the string set ||5;13;15|| is the basis for the conjugate of RD(2). Its basic scale string is <1111121111112> and, using <5;13> = <23233> as the generic string, the members of the WARPSET can easily be calculated: {<23334>, <24234>, ..., <33333>}. Presence and location of the two pairs of Riemann covers can now easily be determined.
9. Extension of David Lewin’s Riemann Systems
[9.1] Returning to Riemann diatonic systems, we now procede to reconcile our “topological” approach with David Lewin’s “tonal function” approach. Consider first Lewin’s definition which we have been studiously avoiding until now: “By a Riemann System (RS) we shall understand an ordered triple (T,d,m), where T is a pitch class and d and m are intervals, subject to the restrictions that [neither d nor m is 0 and m does not equal d].”(10) He then procedes to define the tonic triad as the unordered set {T,T+m,T+d}. This, and the rest of the relationships investigated by Lewin, can be transported to RD(1) since, for example, his RS (T,7,4) produces the triad {0,0+4,0+7} = {0,4,7} which coincides with 0t in RD(1). But can the Lewin-Riemann concept of chord construction (and concomitant relationships) be modified to fit any RD system? Using 0r = {0,4,10,13,19} as a test chord in RD(2) we guess that (T,13,m) might be an irredundant RS since int13 seems to fulfill a “dominant” function. But what do we make of the quality-determining “mediant interval” m? And how do we generate the other three chord members? The answers to these questions will lead us, at the end of our study, to some bizarre (but nevertheless plausible) conclusions about diatonic systems.
[9.2] Interestingly, any of the four (apex) pentachords (privileged as “tonic” by the definition of a Riemann cover) in RD(2) can be constructed from the RS triple (T,d=13,m=9) as follows:
red: {T, T+d,T+d-m,T+d-2m,T+d-3m}
green: {T,T+m, T+d,T+d-m,T+d-2m }
yellow:{T,T+m,T+2m, T+d,T+d-m }
blue: {T,T+m,T+2m,T+3m,T+d }
The spacing in each set is used to draw attention to the grouping of elements. The colors on the left are randomly assigned “shape” or “chord quality” or “mode” designations analogous to “major” and “minor.” Note that each set contains both T and T+d, as we would expect. But whereas in the simpler triadic system the only other element is T+m, here there is a combination of three additional elements, each with the form T+km or T+d-km (k=0,1,2,3); that is, T and T+d are “anchor points” to which positive and negative integral multiples of m are added.
[9.3] Setting T=0,15,6,21, we may now calculate the four basic Lewin- Riemann tonic pentachords in the scale {0,2,4,6,8,10,11,13,15,17,19,21,23}.
red: set T=0
{0,0+13,0+13-9,0+13-18,0+13-27} mod 24
= {0,13,4,19,10}
(= 0r)
green: set T=15
{15,15+9,15+13,15+13-9,15+13-18} mod 24
= {15,0,4,19,10}
(= 15s’)
yellow: set T=6
{6,6+9,6+18,6+13,6+13-9} mod 24
= {6,15,0,19,10}
(= 6s)
blue: set T=21
{21,21+9,21+18,21+27,21+13} mod 24
= {21,6,15,0,10}
(= 21r’)
[9.4] “Dominant” and “subdominant” pentachords related to each of the four basic pentachords can be found by adding 13 and -13 (=11), respectively, to each T-value in [9.3]. Thus there are four sets of primary pentachords in this extended RS. Lewin’s secondary chords can similarly be transported, but we will concentrate here on the primary chords.
[9.5] A Lewin-Riemann System (LRS) may be found in any RD system by generalizing [9.2] in the following way. If ||x;y;z|| is an RD WARPSET (where x is odd and > 1, y = 3x-2, and z = 6(x-1)), then an embedded LRS can be identified as the ordered triple (T,d,m) where T is a pitch class (mod z), d=y, and m=y-4. A tonic x-ad of the RS (T,d,m) is the unordered set TON = {T+fm,T+d-gm}, a dominant x-ad is DOM = {T+d+fm,T+2d-gm}, and a subdominant x-ad is SUB = {T-d+fm,T-gm}, where f = 0,...,a and g = 0,...,b are related by a+b = x-2.
[9.6] The triple (TON,DOM,SUB) generated by the RS (T,7,4) can be traditionally interpreted as defining a chord-generated “key” in relationship to the pitch class T. Thus the RS (T=3,d=7,m=4) implies the “key”
KEY(E ,+) DEF {(E ,+).&.(B ,+).&.(A ,+)}
with (E ,+) stipulated as “the harmonic
goal”.
This in turn implies the “relative key”
KEY(C,-) DEF {(C,-),&.(G,-).&.(F,-)}
with (C,-) stipulated as “the harmonic
goal”.
Looking back at the four basic (T,13,9) chords listed in [9.3] and generating their respective dominants and subdominants, using string notation for clarity we can create the following modal key relationships (“/” here denotes “with”).
KEY(0,red) DEF [{0r.&.11r.&.13r} / 0r DEF “goal” KEY0]
KEY(15,green) DEF [{15s’.&.2s’.&.4s’} / 15s’ DEF “goal” KEY1]
KEY(6,yellow) DEF [{6s.&.17s.&.19s} / 6s DEF “goal” KEY2]
KEY(21,blue) DEF [{21r’,.&.8r’.&.10r’} / 21r’ DEF “goal” KEY3]
Note that each tonic (“goal” KEYk) is generated by our original choice for the pitch class T = 0 by running through the values of a (see [9.5])
a = 0, KEY0 = T - (0 X m) = T - 0 = 0
a = 1, KEY1 = T - (1 X m) = T - 9 = 15
a = 2, KEY2 = T - (2 X m) = T - 18 = 6
a = 3, KEY3 = T - (3 X m) = T - 27 = -3 (mod24) = 21
This may all be generalized as follows.
[9.7] HYPERKEYS. Given the variables stipulated in [9.5],
- a “key stipulation” generated by the LRS (T,d,m) is defined as KEYa = T-am
(mod z)
- a hyperkey structure KEY(KEYa,name) is defined as [{TON.&.DOM.&.SUB} / TON DEF
“goal” KEYa], where name is purely referential and can be chosen at random.
- the “relative” of (KEYa,name1) is (KEYb,name2), where b = x-2-a from [9.5].
[9.8] NB: [9.5] makes a significant modification to the original Lewin definition quoted in [9.1]. Whereas RS (tri)chords are always oriented toward T as a “monopole,” in order to extend this system into higher order RDs we have been forced to define the generalized LRS chord as bipolar, i.e., the x-2 mediants are added to and/or subtracted from either T or T+d. The effect of this is to destroy the uniformly one-directional nature of Riemann’s original concept where the entire chord is described as “up” or “down” from a root/tonic. However it is possible to “save the appearances” with respect to up-ness and down-ness in higher RD systems.
[9.9] OPERATIONS IN LRS. In this section we have thus far been concentrating on definitions in order to transport RS structures into higher RD systems as LRS structures. But the heart of Lewin’s Riemann System is the family of operations
IDENT (identity)
CONJ (conjugate)
TDINV (tonic-dominant
inversion)
RET (retrograde)
collectively called the “serial group” of operations (GSER).(11) These operations on (T,d,m) consist essentially of alternations of three elements:
location (whether
the root is T or T+d)
polarity (whether d and
m are positive or negative)
mode (whether the
mediant element is m or m’=d-m).
So GSER consists of
IDENT: change
nothing,
CONJ: keep T and change
mode,
TDINV: add d to T and
change polarity (of d and m),
RET: add d to T and
change both polarity (of d and m) and mode.
Thus for RS (0,7,4), if the original triad is X = (0,4,7) = C major
IDENT(X) = (0,4,7) =
C major
CONJ(X) = (0,3,7) = C
minor
TDINV(X) = (7,3,0) =
dual G minor
RET(X) = (7,4,0) = dual
G major.
But our revised definition for an LRS keeps the mode constant to accomodate multiple mediant elements, centering instead on the separate polarity alterations of d and m, a “+” value being measured from T and a “-” value being measured from T+d. Thus the revised family of operations, GSER*, can be described
IDENT: change
nothing,
CONJ: change polarity
of m,
TDINV: add d to T and
change polarity of both d and m,
RET: add d to T and
change polarity of d.
[9.10] The reader may verify that GSER* produces the same set of chords as GSER in the previous example. But to illustrate that GSER* generalizes to higher RD systems, consider the LRS (T=0,d=13,m=9) and generate a “green” set as defined in [9.3]: X = (T,T+m; T+d-2m,T+d-m,T+d) = (0,9; 19,4,13). Here we have reversed the order of elements on the right to illustrate the pentachord’s bipolar structure,
(T)-->(T+m) (T+d-2m)<--(T+d-m)<--(T+d),
\ /
\ /
\--------------->---------------/
a short right arrow indicating +9, a short left arrow indicating -9, and the long right arrow indicating +13 (all mod 24). GSER* then yields:
IDENT(X) = (0,9; 19,4,13) = 0-green
CONJ(X) = (0,9,18; 4,13) = 0-yellow
TDINV(X) = (13,4; 18,9,0) = dual 13-yellow
RET(X) = (13,4,19; 9,0) = dual 13-green.
[9.11] The arrangement which places T on the far left and T+d on the far right with the
set of mediant elements in between will be called
the canonical arrangement of an LRS chord. In the above example, the intervals between the
elements of the canonically ordered X, read left
to right, form a substring /9A99/, where A=10 (just why this is called a substring here
will be evident shortly). Since the “subdominant” and “dominant”
pentachords which join X to form the primary chords of the system each share a common
(polar) tone with X, the substring of the canonical (sub)string form of the entire
structure (11,20,6,15,0,9,19,4,13,22,8,17,2) is /9A999A999A99/.
[9.12] THE SHIFT OPERATION. If we now clone the canonical substring /9t99/ an indefinite number of times we have the infinite repeating string Q = <...9A999A999A999A999A99...>. We may then directly apply Lewin’s definition of the SHIFT operation: “Given an integer N ... we will define a formal operation SHIFT(N) which operates on any given [L]RS to produce a transformed [L]RS whose canonical listing is ‘shifted N places’ from that of the given system.”(12)
[9.13] For a triadic system such as (T,7,4) in C12, K is an alternation of m and d-m, <...343434...>. When paired with appropriate pitch classes, e.g., ( ...g Bb d F a C e G b D f# A ...), SHIFT in effect produces modulations. But even more, it describes a functional relationship between virtually any pair of diatonic chords. For instance, SHIFT(+2) applied to segment (B d F a C e G) modulates to (F a C e G b D), i.e., from F major to C major (or from a B -13th chord to an F-13th chord). In RD(2), SHIFT produces analogous pairing relationships.
[9.14] Returning to numerical notation for chord elements (mod 24 for clarity) and assigning 0 to reflect the example in [9.3], the string Q= <...9A999A999A999A999...> produces the canonically ordered structure
(...11,20,6,15,0,9,19,4,13,22,8,17,2,11,21,6,15,0,...).
Again using red, green, yellow, and blue from [9.3] as mode designations, 0-green
indicates the canonic structure (11,20,6,15,0,9,19,4,13,22,8,17,2) with the substring
/9A999A999A99/ which can be rearranged to disclose the “0-green scale”
{0,2,4,6,8,9,11,13,15,17,19,20,22} with the C24 string <2222122222122>.
[9.15] SHIFT(+1) applied to 0-green produces SHIFT(+1)(0-green) = (20,6,15,0,9,19,4,13,22,8,17,2,11) = 9-yellow with the substring /A999A999A999/. The “9-yellow scale” {9,11,13,15,17,19,20,22,0,2,4,6,8} with the string <2222212222221> shows that SHIFT(+1) here has kept all of 0-green’s pcs but shifted the “tonic” from pc0 to pc9 and rotated the string, i.e., produced a “modal modulation.”
[9.16] On the other hand, SHIFT(+2)(0-green) = SHIFT(+1)(9-yellow) = 19-blue = (6,15,0,9,19,4,13,22,8,17,2,11,21) has the substring /999A999A999A/ and represents a “chromatic-modal modulation” with respect to both 0-green and 9-yellow. The “19-blue scale” is {19,21,22,0,2,4,6,8,9,11,13,15,17} with string <2122222122222>; its string is not only a different rotation of <13;24> than either 0-green or 9-yellow, but it also adds pc21 which neither of the other two systems (keys) contains.
[9.17] As we have seen, by modifying Lewin’s original definitions for Riemann Systems, both the group of operations GSER (as GSER*) and the operation SHIFT(N) are preserved in the hyperdiatonic system RD(2). Extending to larger hyperdiatonic systems, the following progression is easily verified:
RD(1) <-->
(T,7,3) in C12
RD(2) <-->
(T,13,9) in C24
RD(3) <-->
(T,19,15) in C36
...
...
RD(n) <-->
(T,7+6(n-1),3+6(n-1)) in C12n
It is left as an exercise to determine the LRS canonical form of the substring supporting any basic chord in RD(n), i.e., to complete the following: (T,7,3) --> /43/; (T,13,9) --> /A999/; (T,19,15) --> /?/; (T,?,?) --> /?/.
***************
INSTEAD OF A CONCLUSION.
There is no truth beyond magic....
One, when you’ve discovered the truth ...
it does have the most extraordinary
magical quality about it. It’s the
payoff, to recognize the deep order ...,
you feel you are in touch with something
fundamental. But there’s also a poetic
sense in it: reality is strange. Many
people think reality is prosaic. I don’t.
We don’t explain things away....
We get closer to the mystery.Brian Goodwin, theoretical biologist,
quoted in Roger Lewin, Complexity:
life at the edge of chaos
(Macmillan, 1992)
Despite the promise made at the end of Part I, I must break off the development at this
point solely for reasons of space, leaving the promise only partially fulfilled. This
study grew over the past two years from a simple premise, the development of which I
foolishly believed would be at least short if not sweet. (I have now learned a valuable
lesson about simple premises and promises.) Though I had not planned it this way, I will
have to publish the conclusion to this tonal fantasy in the future as Part III. But I will
take my time with it, perhaps to savor it.
Part III begins as a study in hyperdiatonic voice leading based on Richard Cohn’s parsimonious chord pairs and Eytan Agmon’s efficient linear transformations. These voice-leading considerations then force some startling, even bizarre, conclusions about the nature of higher order hyperdiatonic systems. While maintaining much of the usual diatonic’s salient features, a fourth-order hyperdiatonic system contains “hypertones,” sets which behave much like single tones in the usual diatonic (this was first hinted at in [9.1] with the “mediant problem”). This behavior then implies a nascent theory of “counterset” which might arise through compositional praxis. But, even without an existing body of hyperdiatonic works, by re-examining Schenker’s “axioms” it is possible to devise a “hyper-Schenkerian conjecture” which asserts that counterpoints generally arise as more or less natural products of white note systems, rather than magically as the result of a fortuitous history. Examination of this idea will, finally, conclude Part III of this particular fantasy. But there is more; much more, I think. While examining the “simple premise” in relation to tonal theory, it has become increasingly obvious to me that the WARP function, which effectively transforms any musical structure from one “space” to another, can be useful in the study of (hyper)atonal structures. This idea is now a work-in-progress and has already provided some startling connections and pointed to unsolved problems. But for now I am convinced enough of WARP’s power to flush out invariants, that I am willing to make the following statement, not because I think it will necessarily turn out to be “true,” but because I think it is the right goal for speculative theory. Just as there are abstract geometries which can only be reached by studying their various models, there are abstract musics which can only be reached by studying their various models. It may be that we will ultimately learn that there is only one abstract music; and, at least in this sense if no other, distinctions melt away: There is only ONE music.
Stephen Soderberg
Library of Congress
Music Division
101 Independence Avenue SE
Washington, DC 20540
ssod@loc.gov
Footnotes
1. John Clough and Jack Douthett, “Maximally Even Sets,” Journal of
Music Theory 35.1 & 2 (1991): 96.
Return to text
2. There is some redundancy in this notation since any necklace class
has any number of ME tokens; for example, <(7;12)> represents the same necklace
class as, say, <(7;9)> and <(7;16)>. While it would be more cumbersome and
less intuitive, this notation could be improved by partitioning all ME strings with
M(m,x,k) defined as all strings of the form <m;xm%k> where m,x,k are integers with m
>= 1; x = 1,2,...; k <= [[m/2]]; xm%y >= m; and % stands for “plus or
minus.” N(m,x,k) would then represent all necklaces which can be derived from any
member of M(m,x,k) by substitution. Or, using the “generating” case and the
above notation, we might simply use N(m,k) defined as <(m;m+k)>. Thus <7;12>,
<7;9>, <7;16>, as well as <1171117> and so on, all belong to the
necklace class N(7,2) = <(7;9)> = <aabaaab>.
Return to text
3. This particular WARPSET presents a situation that occasionally
arises when resultant strings are symmetric. Note that a’ is a circular permutation of a,
i.e., a and a’ represent the same shape, so for any p in C13, (p,a’) = (p-4,a) (mod 13)
(see [1.13] in Part I). If we “canonize” a = <445> as the
“correct” string form and require that all a-based structures be put in that
“root position” form, the CHORDSET given in [5.6] must be abandoned for
{0a,1a,11a,4b,5b,6b,7a,4a,5a,11b,12b). This in turn makes scale elements 4, 5, and 11 into
roots which can be associated with both a and b strings, whereas scale elements 2, 8, and
9 can’t be associated as roots with any chords.
Return to text
4. Clough and Douthett, op. cit., pp.170-71.
Return to text
5. “System” is used here in the sense of the ordered triple
of [2.25] in Part I. “Diatonic system” may be confused with that term as used by
C&D (---) and Agmon (---), and for that reason we will mostly use the term
“Riemann Diatonic System” introduced below.
Return to text
6. Diatonic tetrachords (e.g., the dominant 7th-chord) are not
included here since they would unduly complicate the present study. But the reader may
want to keep these important structures in mind as we procede since they present an
interesting dilemma. In the usual diatonic system, clearly one could view a 7th-chord as
either a triad with an added third or the complement of a triad with respect to
the diatonic scale (at the end of the day they produce the same structure). However, as
the reader may note after reading about the next RD system, these two possible
construction principles, when lifted into RD(2), produce different results. In RD(2) the
basic structure is a 5-note chord. If we use the additive principle, the
“hyper7th-chord” will have six notes. But if we use the complement principle,
the “hyper7th-chord” will have eight notes.
Return to text
7. The reader is invited to generate and compare the AVLINTs for the
three other possible triadic white note systems which can be associated with the usual
diatonic string using g = <115>, <133> (necklaces) or <124>
(asymmetric). It is then an interesting exercise to search for non-diatonic scale strings
for each of these generic strings which might be profitably employed as a basis for
compositional praxis (both inside and outside C12).
Return to text
8. Clearly the converse, a preference for maximal variety coupled
with a secondary desire to discover as much symmetry as possible, is most attainable by
choosing COVER2 -- or by choosing neither or both. In the larger sense, if we were to
adopt a preference for variety throughout, we could have stopped with Part I since, when
we find ourselves in any (structured) musical universe, what we can say about any string
can be said about symmetric strings as well, and cover covariance is simply an objective
fact associated with whatever system we happen to find ourselves in at the moment. But in
beginning Part II by focusing on necklaces and then on maximal evenness and (hyper)diatony
we already (perhaps covertly) stated a preference for symetric structures which a fortiori
guides our present and subsequent choices.
Return to text
9. David Lewin, “A Formalized Theory of Generalized Tonal
Functions,” Journal of Music Theory 26.1 (1982).
Return to text
10. Lewin, op. cit., 26.
Return to text
11. Lewin, op. cit., 37–39.
Return to text
12. Lewin, op. cit., 48.
Return to text
Copyright Statement
Copyright © 1999 by the Society for Music Theory. All rights reserved.
[1] Copyrights for individual items published in Music Theory Online (MTO) are held by their authors. Items appearing in MTO may be saved and stored in electronic or paper form, and may be shared among individuals for purposes of scholarly research or discussion, but may not be republished in any form, electronic or print, without prior, written permission from the author(s), and advance notification of the editors of MTO.
[2] Any redistributed form of items published in MTO must include the following information in a form appropriate to the medium in which the items are to appear:
This item appeared in Music Theory Online in [VOLUME #, ISSUE #] on [DAY/MONTH/YEAR]. It was authored by [FULL NAME, EMAIL ADDRESS], with whose written permission it is reprinted here.
[3] Libraries may archive issues of MTO in electronic or paper form for public access so long as each issue is stored in its entirety, and no access fee is charged. Exceptions to these requirements must be approved in writing by the editors of MTO, who will act in accordance with the decisions of the Society for Music Theory.
This document and all portions thereof are protected by U.S. and international copyright laws. Material contained herein may be copied and/or distributed for research purposes only.
Prepared by Brent Yorgason and Rebecca Flore, Editorial Assistants